Passwords Are Dead
Remember when passwords were like the ultimate lock on your digital door? Well, imagine if you were using a paperclip to secure a vault of gold. Yeah, it’s that bad.
By Jason Patel
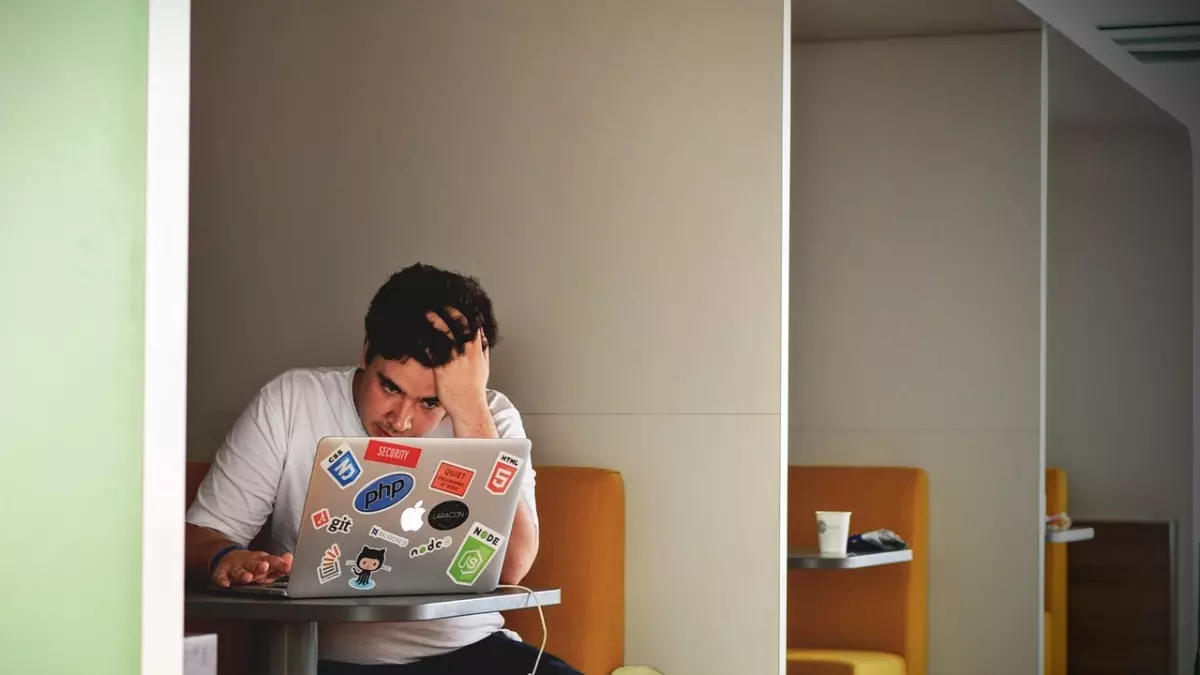
Passwords, once the cornerstone of cybersecurity, are now the equivalent of a rusty padlock on a treasure chest. Hackers have evolved, and so have their methods. The problem? Most of us haven’t. We’re still clinging to passwords like they’re the holy grail of security, but in reality, they’re more like a ticking time bomb.
Let’s break it down. Passwords are vulnerable for a few reasons. First, most people use weak passwords. You know the type: “password123” or “qwerty.” Second, even if you’re a password ninja with a 16-character string of randomness, hackers have tools like brute force attacks and password-cracking algorithms that can eventually break through. And third, even if your password is strong and unique, it can still be stolen through phishing attacks or data breaches. So, yeah, passwords alone? Not cutting it anymore.
The Rise of Credential Stuffing
Here’s where things get even scarier. Ever heard of credential stuffing? It’s a hacker’s dream and your worst nightmare. When a major data breach happens (and let’s face it, they happen all the time), hackers get their hands on millions of usernames and passwords. They then use automated tools to try those credentials on other websites. Why? Because people reuse passwords. A lot. So, if your password was leaked in a breach from, say, a random shopping site, hackers will try that same password on your email, bank, or social media accounts. And boom—they’re in.
Credential stuffing attacks are on the rise, and they’re incredibly effective because, let’s be honest, most of us are lazy when it comes to password management. We reuse passwords across multiple sites, and hackers know it. They’re counting on it.
Two-Factor Authentication to the Rescue?
Okay, so if passwords are so terrible, what’s the solution? Enter two-factor authentication (2FA). You’ve probably heard of it, maybe even use it, but let me tell you—it’s a game-changer. 2FA adds an extra layer of security by requiring not just something you know (your password), but something you have (like your phone) or something you are (like your fingerprint).
Here’s how it works: even if a hacker gets your password, they still can’t access your account without the second factor. It’s like having a second lock on your door, but this one’s made of steel, not paperclips. Sure, it’s not foolproof—nothing is—but it’s a heck of a lot better than relying on passwords alone.
Beyond 2FA: The Future of Passwordless Security
But wait, there’s more! The future of cybersecurity is looking beyond passwords entirely. Passwordless authentication is becoming a reality, and it’s about time. Technologies like biometrics (think facial recognition or fingerprint scans) and hardware tokens (like YubiKeys) are leading the charge. These methods are far more secure because they can’t be easily stolen or guessed like a password can.
Biometrics, in particular, are gaining traction. After all, it’s a lot harder for a hacker to steal your face or fingerprint than it is to steal your password. And hardware tokens? They’re like carrying a digital key that only you possess. Even if a hacker has your password, they can’t get in without the token.
Of course, no system is perfect. Biometrics can be spoofed, and hardware tokens can be lost. But when combined with other security measures, they offer a much stronger defense than passwords alone ever could.
What You Can Do Right Now
So, what’s the takeaway here? First, stop relying on passwords alone. If you haven’t already, enable two-factor authentication on all your important accounts. It’s a simple step that can make a huge difference in your security.
Second, consider using a password manager. These tools generate and store complex, unique passwords for each of your accounts, so you don’t have to remember them all. Plus, they’ll alert you if any of your passwords have been compromised in a data breach.
And finally, keep an eye on the future. Passwordless authentication is coming, and it’s going to change the game. Start exploring options like biometrics or hardware tokens now, so you’re ahead of the curve when passwords finally go the way of the dinosaur.
In the end, it’s clear: passwords are no longer enough. But with the right tools and a little vigilance, you can stay one step ahead of the hackers.