Outdated Protocols
Imagine you're driving a car from the 90s on a modern highway, surrounded by sleek, high-tech vehicles. Sure, it still runs, but is it really safe?

By Kevin Lee
Cybersecurity protocols are a lot like that old car. They might have been cutting-edge when they were first implemented, but in today’s rapidly evolving digital landscape, they’re more of a liability than an asset. What once protected your network from cyber threats is now a rusty shield, full of holes that modern hackers can easily exploit.
Back in the early 2000s, cybersecurity was a simpler game. Firewalls, antivirus software, and basic encryption were enough to keep most threats at bay. Hackers were less sophisticated, and businesses could get away with updating their security protocols every few years. But as technology advanced, so did the methods of cybercriminals. Today, relying on outdated protocols is like leaving your front door wide open in a neighborhood full of burglars.
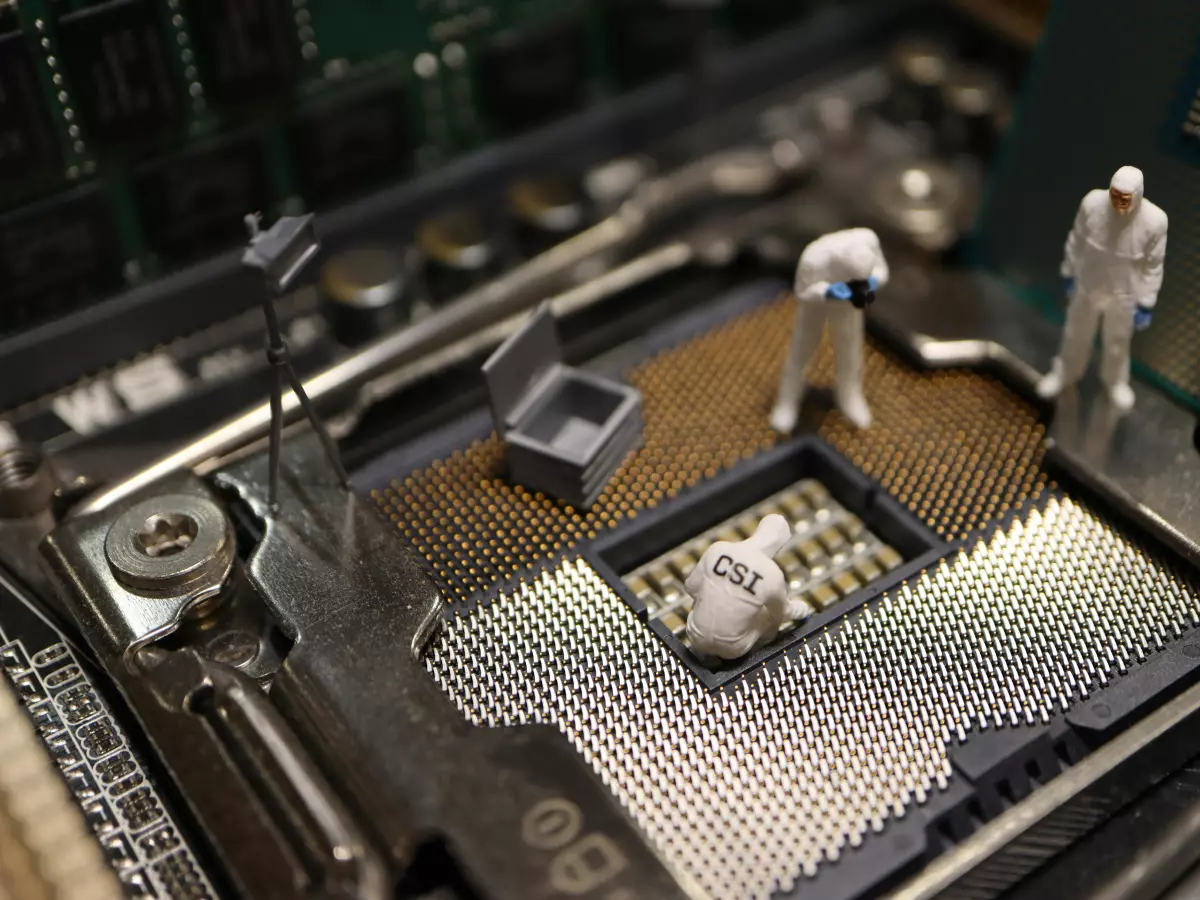
Fast forward to the present, and the cybersecurity landscape has become a battlefield. Hackers are no longer lone wolves working out of their basements. They’re part of organized crime syndicates, state-sponsored groups, and even AI-powered bots. These cybercriminals have access to tools and techniques that can bypass outdated protocols with ease. If your business is still relying on security measures from five or ten years ago, you’re essentially inviting them in.
Why Outdated Protocols Are a Major Risk
One of the biggest dangers of outdated cybersecurity protocols is that they’re no longer designed to handle modern threats. Think about it: the types of attacks we’re seeing today—ransomware, phishing, and DDoS attacks—didn’t even exist when many of these protocols were first developed. As a result, they’re not equipped to detect or defend against these new forms of cybercrime.
Another issue is that outdated protocols often lack the ability to integrate with newer technologies. For example, many older systems don’t support multi-factor authentication (MFA), which has become a critical component of modern cybersecurity. Without MFA, your network is far more vulnerable to brute force attacks and credential theft.
And let’s not forget about encryption. Encryption standards have come a long way in the past decade, but if you’re still using outdated encryption protocols, your data is at risk. Hackers have developed techniques to crack older encryption methods, leaving your sensitive information exposed.
The Cost of Complacency
So why do so many businesses continue to rely on outdated cybersecurity protocols? The answer is simple: complacency. It’s easy to fall into the trap of thinking, “If it ain’t broke, don’t fix it.” But in the world of cybersecurity, that mindset can be disastrous.
Updating your cybersecurity protocols can be time-consuming and expensive, but the cost of a data breach is far higher. According to a report by IBM, the average cost of a data breach in the U.S. is $9.44 million. That’s not just a financial hit—it’s a blow to your reputation, your customer trust, and your ability to operate as a business.
And it’s not just large corporations that are at risk. Small and medium-sized businesses (SMBs) are often targeted precisely because they’re more likely to have outdated security measures in place. Hackers know that SMBs don’t have the same resources as larger companies, making them easier targets.
How to Stay Ahead of the Game
The good news is that you don’t have to be a sitting duck. By regularly updating your cybersecurity protocols, you can stay one step ahead of cybercriminals. Here are a few steps you can take to ensure your network is protected:
- Conduct regular security audits: Make it a habit to review your cybersecurity protocols at least once a year. Identify any outdated systems and replace them with modern solutions.
- Implement multi-factor authentication: MFA is one of the most effective ways to protect your network from unauthorized access. If your current protocols don’t support MFA, it’s time for an upgrade.
- Stay informed about new threats: Cybercriminals are constantly developing new methods of attack. Stay up to date on the latest threats and adjust your security measures accordingly.
- Invest in employee training: Human error is one of the leading causes of data breaches. Make sure your employees are trained on the latest cybersecurity best practices.
- Use modern encryption standards: Ensure that your data is protected with the latest encryption protocols. Outdated encryption is an open invitation for hackers.
By taking these steps, you can significantly reduce your risk of a cyberattack. Remember, cybersecurity is not a one-time investment—it’s an ongoing process that requires constant attention and adaptation.
So, the next time you’re tempted to put off that security update, think about that old car on the highway. Sure, it might still run, but do you really want to take the risk?